| 일 | 월 | 화 | 수 | 목 | 금 | 토 |
|---|---|---|---|---|---|---|
| 1 | 2 | 3 | 4 | |||
| 5 | 6 | 7 | 8 | 9 | 10 | 11 |
| 12 | 13 | 14 | 15 | 16 | 17 | 18 |
| 19 | 20 | 21 | 22 | 23 | 24 | 25 |
| 26 | 27 | 28 | 29 | 30 | 31 |
- Leviathan
- 포너블
- 워게임
- pwn.college
- write up
- 리눅스
- 커널
- C++
- css
- multiplexing
- 리눅스커널
- 프로그래밍
- Bandit
- C언어
- wargame
- 시스템해킹
- kernel
- 리버싱
- 하드링크
- 리눅스 커널
- radare2
- Pwnable.kr
- 어셈블리어
- 시스템 프로그래밍
- 알고리즘
- 시스템프로그래밍
- 컴퓨터구조
- pwncollege
- 시그널
- 시스템
- Today
- Total
Computer Security
#18 Wargame bandit 15 (Level30 ~ 33(End)), git show-ref, git 파일 추가 본문
#18 Wargame bandit 15 (Level30 ~ 33(End)), git show-ref, git 파일 추가
쿠리 Kuri 2022. 7. 25. 18:30Level30 -> Level31
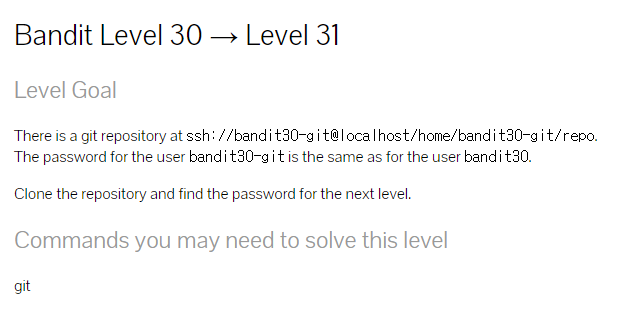
ssh://bandit30-git@localhost/home/bandit30-git/repo에 git 저장소가 있습니다.
bandit30-git 사용자의 비밀번호는 bandit30 사용자의 비밀번호와 동일합니다.
저장소를 복제하고 다음 레벨의 비밀번호를 찾으십시오.1.이전문제와 비슷한 문제인 것 같다. cd 명령어로 tmp 디렉토리에 접근한 뒤, mkdir 을 이용해 banduit30이라는 디렉토리를 하나 만들어 bandit30에 접근하자.
bandit30@bandit:~$ ls -al
total 20
drwxr-xr-x 2 root root 4096 May 7 2020 .
drwxr-xr-x 41 root root 4096 May 7 2020 ..
-rw-r--r-- 1 root root 220 May 15 2017 .bash_logout
-rw-r--r-- 1 root root 3526 May 15 2017 .bashrc
-rw-r--r-- 1 root root 675 May 15 2017 .profilebandit30@bandit:~$ cd /tmp
bandit30@bandit:/tmp$ mkdir bandit30
bandit30@bandit:/tmp$ cd bandit30
2. 이제 이 bandit30안에 git clone명령어를 이용해 복제를 한다.
bandit30@bandit:/tmp/bandit30$ git clone ssh://bandit30-git@localhost/home/bandi t30-git/repo
Cloning into 'repo'...
Could not create directory '/home/bandit30/.ssh'.
The authenticity of host 'localhost (127.0.0.1)' can't be established.
ECDSA key fingerprint is SHA256:98UL0ZWr85496EtCRkKlo20X3OPnyPSB5tB5RPbhczc.
Are you sure you want to continue connecting (yes/no)? yes
Failed to add the host to the list of known hosts (/home/bandit30/.ssh/known_hos ts).
This is a OverTheWire game server. More information on http://www.overthewire.or g/wargames
bandit30-git@localhost's password:
remote: Counting objects: 4, done.
remote: Total 4 (delta 0), reused 0 (delta 0)
Receiving objects: 100% (4/4), done.
3.ls 명령어로 확인 해보니 README.md가 존재한다. 읽어 보자.
bandit30@bandit:/tmp/bandit30/repo$ cat README.md
just an epmty file... muahaha
4.이번엔 아예 아무것도 없어 git log 로 확인해봤지만 이것 역시 힌트가 될 만한 것이 없다.
bandit30@bandit:/tmp/bandit30/repo$ git log
commit 3aefa229469b7ba1cc08203e5d8fa299354c496b
Author: Ben Dover <noone@overthewire.org>
Date: Thu May 7 20:14:54 2020 +0200
initial commit of README.md
5.git branch를 이용해 branch를 확인 해 봤지만, 뭐 이거 이외에 다른 곳이 없어 보인다.
bandit30@bandit:/tmp/bandit30/repo$ git branch -a
* master
remotes/origin/HEAD -> origin/master
remotes/origin/master
6.혹시나 누락된 branch가 있는지 git show-ref 명령어로 확인 해본다.
bandit30@bandit:/tmp/bandit30/repo$ git show-ref
3aefa229469b7ba1cc08203e5d8fa299354c496b refs/heads/master
3aefa229469b7ba1cc08203e5d8fa299354c496b refs/remotes/origin/HEAD
3aefa229469b7ba1cc08203e5d8fa299354c496b refs/remotes/origin/master
f17132340e8ee6c159e0a4a6bc6f80e1da3b1aea refs/tags/secret
7. refs/tags/secret 정말 수상한 secret 이보여 git show f17132340e8ee6c159e0a4a6bc6f80e1da3b1aea 로 확인 해봤더니 비밀번호가 나왔다!
bandit30@bandit:/tmp/bandit30/repo$ git show f17132340e8ee6c159e0a4a6bc6f80e1da3b1aea
47e603bb428404d265f59c42920d81e5
8.위에서 얻은 bandit31 비밀번호:47e603bb428404d265f59c42920d81e5 를 이용해 bandit31에 접속하면 성공!
For your convenience we have installed a few usefull tools which you can find
in the following locations:
* gef (https://github.com/hugsy/gef) in /usr/local/gef/
* pwndbg (https://github.com/pwndbg/pwndbg) in /usr/local/pwndbg/
* peda (https://github.com/longld/peda.git) in /usr/local/peda/
* gdbinit (https://github.com/gdbinit/Gdbinit) in /usr/local/gdbinit/
* pwntools (https://github.com/Gallopsled/pwntools)
* radare2 (http://www.radare.org/)
* checksec.sh (http://www.trapkit.de/tools/checksec.html) in /usr/local/bin/checksec.sh
--[ More information ]--
For more information regarding individual wargames, visit
http://www.overthewire.org/wargames/
For support, questions or comments, contact us through IRC on
irc.overthewire.org #wargames.
Enjoy your stay!
bandit31@bandit:~$
Level31 -> Level32

ssh://bandit31-git@localhost/home/bandit31-git/repo에 git 저장소가 있습니다.
bandit31-git 사용자의 비밀번호는 bandit31 사용자의 비밀번호와 동일합니다.
저장소를 복제하고 다음 레벨의 비밀번호를 찾으십시오.1. 이전과 똑같이 저장소를 쭉 복제해서 와준다.
bandit31@bandit:~$ cd /tmp
bandit31@bandit:/tmp$ cd bandit31
-bash: cd: bandit31: No such file or directory
bandit31@bandit:/tmp$ cd
bandit31@bandit:~$ cd /tmp
bandit31@bandit:/tmp$ mkdir bandit31
bandit31@bandit:/tmp$ cd bandit31
bandit31@bandit:/tmp/bandit31$ ls
bandit31@bandit:/tmp/bandit31$ ls -al
total 1992
drwxr-sr-x 2 bandit31 root 4096 Jul 20 20:36 .
drwxrws-wt 1 root root 2031616 Jul 20 20:37 ..
bandit31@bandit:/tmp/bandit31$ git clone ssh://bandit31-git@localhost/home/bandi t31-git/repo
Cloning into 'repo'...
Could not create directory '/home/bandit31/.ssh'.
The authenticity of host 'localhost (127.0.0.1)' can't be established.
ECDSA key fingerprint is SHA256:98UL0ZWr85496EtCRkKlo20X3OPnyPSB5tB5RPbhczc.
Are you sure you want to continue connecting (yes/no)? yes
Failed to add the host to the list of known hosts (/home/bandit31/.ssh/known_hos ts).
This is a OverTheWire game server. More information on http://www.overthewire.or g/wargames
bandit31-git@localhost's password:
remote: Counting objects: 4, done.
remote: Compressing objects: 100% (3/3), done.
remote: Total 4 (delta 0), reused 0 (delta 0)
Receiving objects: 100% (4/4), done.
2.README.md 파일을 읽어보자.
bandit31@bandit:/tmp/bandit31$ ls -al
total 1996
drwxr-sr-x 3 bandit31 root 4096 Jul 20 20:37 .
drwxrws-wt 1 root root 2031616 Jul 20 20:37 ..
drwxr-sr-x 3 bandit31 root 4096 Jul 20 20:37 repo
bandit31@bandit:/tmp/bandit31$ cd repo
bandit31@bandit:/tmp/bandit31/repo$ ls
README.md
bandit31@bandit:/tmp/bandit31/repo$ cat README.md
This time your task is to push a file to the remote repository.
Details:
File name: key.txt
Content: 'May I come in?'
Branch: master원격 저장소 master branch 에 "May I come in?" 이 닮긴 ket.txt 파일을 올리면 다음 비밀번호를 준다 한다.
3.git branch -a 를 이용해 지금 branch가 뭔지 확인한다.
bandit31@bandit:/tmp/bandit31/repo$ git branch -a
* master
remotes/origin/HEAD -> origin/master
remotes/origin/master
4. master 권한이니 바로 ket.txt 파일을 만들어준다.
bandit31@bandit:/tmp/bandit31/repo$ echo "May I come in?" > key.txt
bandit31@bandit:/tmp/bandit31/repo$ ls -al
total 24
drwxr-sr-x 3 bandit31 root 4096 Jul 20 20:39 .
drwxr-sr-x 3 bandit31 root 4096 Jul 20 20:37 ..
drwxr-sr-x 8 bandit31 root 4096 Jul 20 20:37 .git
-rw-r--r-- 1 bandit31 root 6 Jul 20 20:37 .gitignore
-rw-r--r-- 1 bandit31 root 15 Jul 20 20:39 key.txt
-rw-r--r-- 1 bandit31 root 147 Jul 20 20:37 README.md
5. git 저장소에 자료를 추가 및 업로드 하기 위해서는, 일반적으로 add, commit, push의 순서를 따른다. git add -f 를 이용해 ket.txt를 추가해주자. 그다음 commit 까지 해줬다.
bandit31@bandit:/tmp/bandit31/repo$ git add -f key.txt
bandit31@bandit:/tmp/bandit31/repo$ git commit -m "Key add"
[master 50daf2e] Key add
1 file changed, 1 insertion(+)
create mode 100644 key.txt
bandit31@bandit:/tmp/bandit31/repo$ git log
commit 50daf2e10851a46bb30226ef65479bcb8bbc12d3
Author: bandit31 <bandit31@overthewire.org>
Date: Wed Jul 20 20:40:41 2022 +0200
Key add
commit 701b33b545902a670a46088731949ae040983d80
Author: Ben Dover <noone@overthewire.org>
Date: Thu May 7 20:14:56 2020 +0200
initial commit
6. add, commit 을 해줬으니, 마지막으로 우리가 원하는 push를 해준다.
bandit31@bandit:/tmp/bandit31/repo$ git push origin master
Could not create directory '/home/bandit31/.ssh'.
The authenticity of host 'localhost (127.0.0.1)' can't be established.
ECDSA key fingerprint is SHA256:98UL0ZWr85496EtCRkKlo20X3OPnyPSB5tB5RPbhczc.
Are you sure you want to continue connecting (yes/no)? yes
Failed to add the host to the list of known hosts (/home/bandit31/.ssh/known_hos ts).
This is a OverTheWire game server. More information on http://www.overthewire.or g/wargames
bandit31-git@localhost's password:
Counting objects: 3, done.
Delta compression using up to 2 threads.
Compressing objects: 100% (2/2), done.
Writing objects: 100% (3/3), 320 bytes | 0 bytes/s, done.
Total 3 (delta 0), reused 0 (delta 0)
remote: ### Attempting to validate files... ####
remote:
remote: .oOo.oOo.oOo.oOo.oOo.oOo.oOo.oOo.oOo.oOo.
remote:
remote: Well done! Here is the password for the next level:
remote: 56a9bf19c63d650ce78e6ec0354ee45e
remote:
remote: .oOo.oOo.oOo.oOo.oOo.oOo.oOo.oOo.oOo.oOo.
remote:
To ssh://localhost/home/bandit31-git/repo
! [remote rejected] master -> master (pre-receive hook declined)
error: failed to push some refs to 'ssh://bandit31-git@localhost/home/bandit31-g it/repo'
7. 위에서 얻은 bandit32 비밀번호: 56a9bf19c63d650ce78e6ec0354ee45e 로 bandit32에 접속하면 성공!
For your convenience we have installed a few usefull tools which you can find
in the following locations:
* gef (https://github.com/hugsy/gef) in /usr/local/gef/
* pwndbg (https://github.com/pwndbg/pwndbg) in /usr/local/pwndbg/
* peda (https://github.com/longld/peda.git) in /usr/local/peda/
* gdbinit (https://github.com/gdbinit/Gdbinit) in /usr/local/gdbinit/
* pwntools (https://github.com/Gallopsled/pwntools)
* radare2 (http://www.radare.org/)
* checksec.sh (http://www.trapkit.de/tools/checksec.html) in /usr/local/bin/checksec.sh
--[ More information ]--
For more information regarding individual wargames, visit
http://www.overthewire.org/wargames/
For support, questions or comments, contact us through IRC on
irc.overthewire.org #wargames.
Enjoy your stay!
WELCOME TO THE UPPERCASE SHELL
>>
Level32 -> Level33

이 모든 일이 있은 후에 또 탈출할 시간이다. 행운을 빈다.
1. ls 로 기본적인 파일들을 확인해보자.
>> ls
sh: 1: LS: not found모든 문자를 대문자로 바꿔버리는 uppershell 인것 같다.
2. 비밀번호를 얻는다. 얻고 확인해보니, uppershell이 들어있다.
>> $0
$ bash
bandit33@bandit:~$ cat /etc/bandit_pass/bandit33
c9c3199ddf4121b10cf581a98d51caeebandit33@bandit:~$ ls
uppershell
아직 bandit34 그 다음 레벨은 나오지 않았다 한다!! 이렇게 bandit의 모든 문제를 끝냈다!!
'Wargame:Bandit' 카테고리의 다른 글
| #17 Wargame bandit 14 (Level28 ~ Level30), branch,git log,git show,git checkout 명령어 (0) | 2022.07.24 |
|---|---|
| #16 Wargame bandit 13 (Level26 ~ Level28), git clone명령어 (0) | 2022.07.23 |
| #15 Wargame bandit 12 (Level24 ~ Level26), 브루트포스공격,more명령어 (0) | 2022.07.22 |
| #14 Wargame bandit 11 (Level23 ~ Level24), touch,bash,cp (0) | 2022.07.21 |
| #13 Wargame bandit 10 (Level21 ~ Level23), tmp (0) | 2022.07.19 |




